Privacy Guide for Your Apple iOS 15 Devices
Take 5 minutes to run through the settings on your iOS 15 (iPhone and iPad) security settings to ensure you are not leaking data. This article, originally published in the Palm Beach Bar Association Bulletin, explains the steps in a single page article so you can protect your devices and …
Privacy Settings for Zoom Video and Alexa (Palm Beach Bar Association)
While people are working remotely during the COVID-19 pandemic, it is wise to ensure that privacy settings on Zoom and Alexa (and all your devices and applications) are up-to-date. This guide will assist you in correctly securing your Zoom video conferences and Amazon Alexa. Quick note: while this article was …
Protect the Privacy of Your iOS 13 Device (Palm Beach Bar March 2020)
Are you leaking data and revealing your privacy through your iPhone or iPad? In the March 2020 Palm Beach Bar Bulletin, the article, “Protect the Privacy of Your iOS 13 Device,” explains how to ensure you are not unknowingly being tracked, heard, recorded, or located. Written from the perspective of …
Florida Wiretap Act — Reasonable Expectation of Privacy in Someone Else’s House? (Smiley v. Florida)
Corey Smiley was at someone else’s home with an invitation when the discussion turned argumentative, and the other person “began recording the argument on her cell phone… position[ing] the phone in front of Smiley’s face… Smiley questions her about the recording and grabs the phone…” He later was arrested and …
“Valid Grounds for Employment Action” Deemed Not Enough for Stalking Injunction under F.S. 784.048 (Klenk v. Ransom)
Florida’s First District Court of Appeal held today that a respondent’s behavior may be enough for an “employment action” (presumably, for termination due to sexual harassment) but, in this case, was not enough for the “exacting standard” for an injunction against stalking under Florida Statute 748.048. The case is Joseph …
Is Your PC Keeping Your Information Private? Take This 10-Question Quiz
A law firm was behind that largest hack in history. How safe is your desktop or laptop PC? For both home and work, this article presents 10 questions in a quiz format about your security and privacy practices. The article also includes the steps how to find the answers — …
Applying “Old” Laws to New Technology: Smartphones, Recordings, Privacy (at FAU)
Special thanks to attorney / instructor Larry Buck for inviting me to speak to his Florida Atlantic University “Law in the Real World” honors class about my practice, particularly how we apply traditional laws to new, emerging technologies. We discussed: drone regulation First Amendment and social media (US v. Hobgood, …
Don’t Let LinkedIn Follow You Around the Internet (and other privacy settings)
Have you checked your LinkedIn privacy settings? Don’t be fooled with a “I barely even used LinkedIn” attitude. Take 2 minutes. From the article below, here are the key steps: [easier if you have two screens, keep this open and then open your LinkedIn account on your second screen] 1. …
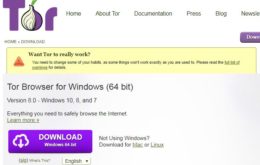
Want to Try Anonymity on the Internet or the Dark Web? New Tor Browser 8 is here… and free
The Tor browser, which helps anonymize your internetting, has been updated to version 8. It’s free and worth having on your desktop. First, these steps simple install a secondary browser on your computer. No spyware. It’s not illegal. It’s just a simple browser. Download it here. It will ask you …
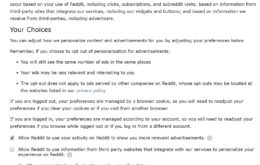
Reddit Automatically Opts You In to Ads & Tracking — Here’s the Privacy Setting Changes to Make Now
While Reddit users tend to be savvy internetters, few of you have likely bothered to check Reddit’s privacy / personalization settings. You need to. Log into Reddit on your PC/Mac, click your user name in the upper right, and select user settings. Note: you cannot make these changes from the …
Protect the Privacy of Your iOS Devices – Palm Beach Bar Association July 2018
The U.S. Supreme Court recently noted, in Carpenter v. US, that Americans “compulsively carry cell phones with them at all times.” For those with iPhones and iPads, have you spent time in Settings protecting your private information? This article from the Palm Beach Bar Association Bulletin, explains ten different ways …
Application of Law to Emerging Technology (at Florida Atlantic University)
Thanks to Professor Larry Buck for inviting me to speak to his Law in the Real World class at FAU about the Application of Law to Emerging Technology. We discussed several cases and scenarios where lawyers and judges are called upon to apply longstanding legal principles to emerging technologies, such …
Can You Record Someone in Florida?
The question of whether you can record someone’s conversation in Florida arises frequently. The answer lies first in a statute and second on the individual circumstances. As a general rule, secretly recording someone in Florida is not going to lead to admissible evidence and could get the person who did …
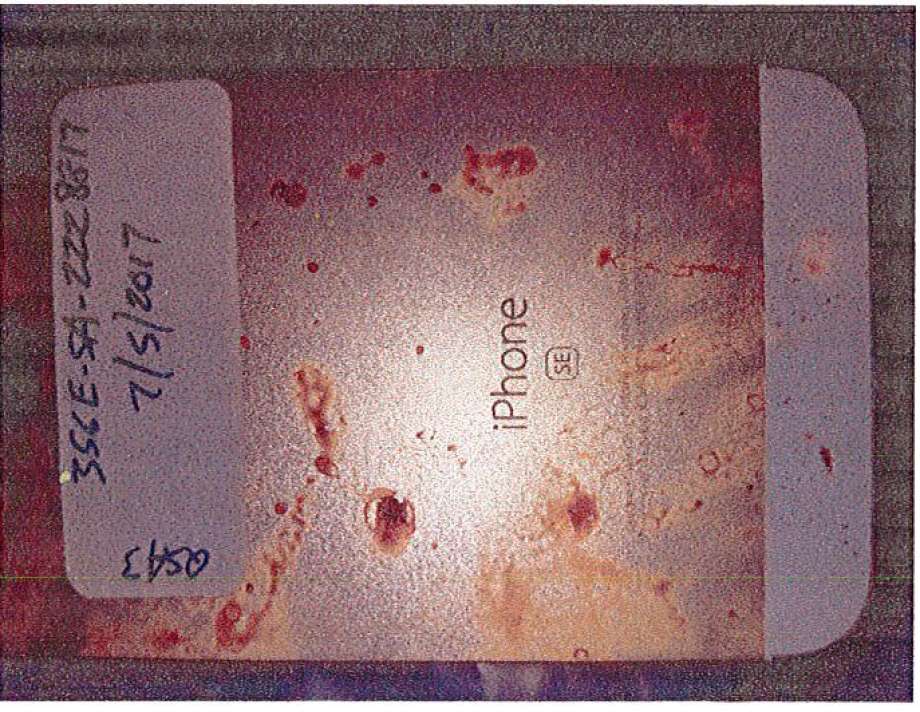
What Does Texas Shooting Case Tell Us About Subpoenas / Warrants for iPhone & iCloud Information?
On November 5, 2017, 26-year old Devin Patrick Kelley allegedly shot and killed 26 people at the First Baptist Church in Sutherland Springs, Texas. Mr. Kelley’s body was reportedly recovered from a Ford Expedition; he was found deceased from a single bullet wound (entering above right ear and exiting …
Edward Snowden: Humorous & Shocking Findings from the [Partially Redacted] House “HPSCI” Report
The House Permanent Select Committee on Intelligence (HPSCI) released in December 2016 a partially-redacted copy of its September 15, 2016 report on its, “Review of the Unauthorized Disclosures of Former National Security Agency Contractor Edward Snowden” (“House Report”). The House Report describes Snowden in the same tenor and tone that the …
Something went wrong with the twitter. Please check your credentials and twitter username in the twitter settings.
Categories
- Arbitration Mediation21
- Causes of Action3
- Clauses from Contracts13
- Conspiracy6
- Constitutional Law44
- Contracts8
- Data Breach34
- Defamation14
- Drones5
- E-discovery26
- Ethics29
- Evidence15
- Florida1
- Injunction2
- Internet5
- iOS38
- JFK6
- Jurisdiction2
- law & order24
- Marijuana12
- Medical Malpractice1
- Nursing Home / Assisted Living4
- Palm Beach2
- Privacy48
- Proposals for Settlement6
- Punitive Damages2
- SCOTUS12
- Social Media67
- Space Law1
- Trial6
- Trump1
- Trusts & Estates1
- Uncategorized61
- Virtual Currency16